3 Workplace Scams Costing Enterprises the Most Money Right Now

Enterprise fraud has changed. Not gradually, but sharply. For years, the biggest threats to businesses were technical: data breaches, ransomware, system exploits. Security teams invested accordingly, and the perimeter got harder to break through.
So attackers stopped trying to break through it. Instead, they started asking someone inside to open the door.
According to the DSIT, 43% of UK businesses experienced a breach or attack in 2024, with AI-driven impersonation now recognised as a mainstream and growing threat. UK Finance also reported that criminals stole £1.17 billion through payment fraud in the UK in 2024 alone.
The three scams behind most of that damage are not new. But AI has made them faster, more convincing, and significantly harder to catch.
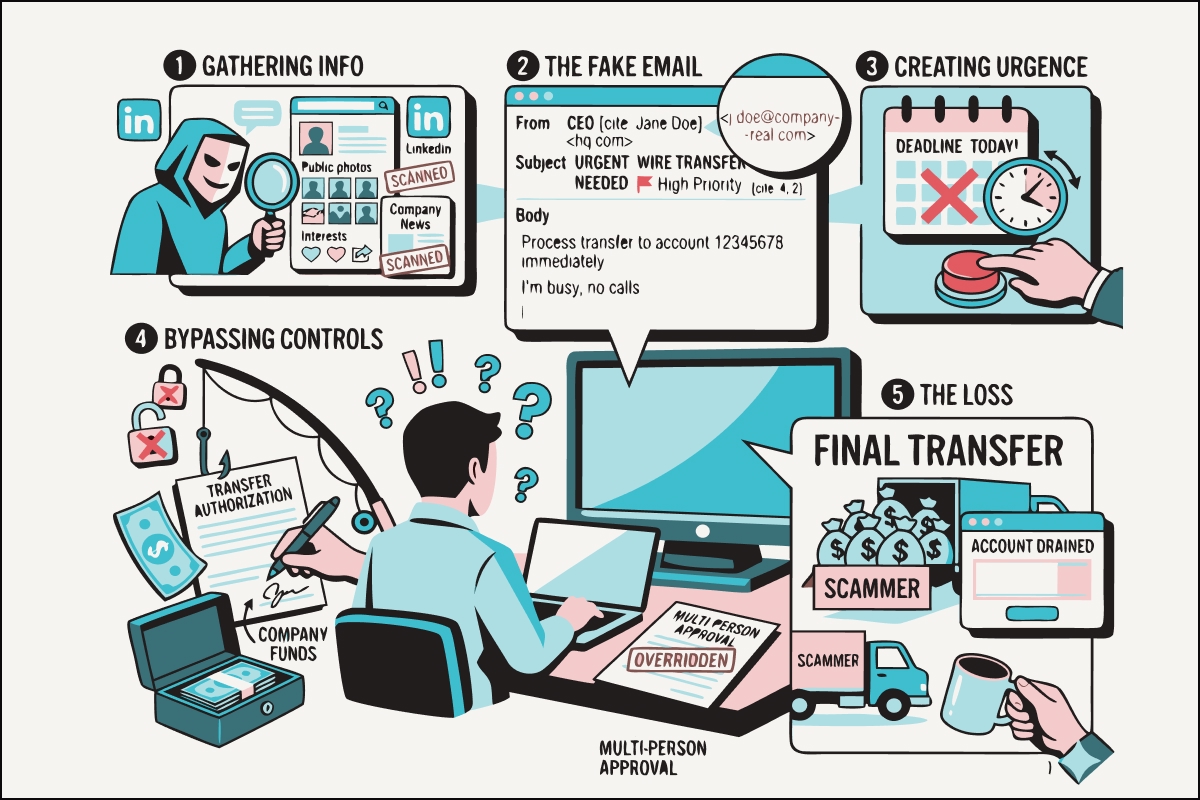
1.0 CEO and Executive Impersonation
1.1 What is CEO impersonation fraud, and how does it work in the workplace?
An attacker impersonates a senior leader, most commonly a CEO, CFO, or department head, to instruct an employee to transfer funds, share credentials, or bypass a standard approval process. The employee acts in good faith. By the time the fraud is discovered, the money is gone. The most common forms of this attack include:
- Urgent payment requests. A message appearing to come from a senior leader instructs an employee to process a payment quickly and outside of normal channels, often with a reason that discourages verification, such as a confidential deal or a time-sensitive window.
- AI voice cloning. Attackers use publicly available audio of an executive, from interviews or company videos, to generate a cloned voice convincing enough to authorise actions over the phone.
- Deepfake video calls. AI-generated video of senior colleagues is used in real-time meetings to instruct staff to take high-risk actions. The face, voice, and professional context all appear legitimate.
- Compromised or spoofed executive email. Attackers replicate an executive's email address or gain access to the real account, then insert fraudulent instructions into active correspondence threads at the right moment.
Each method exploits the same instinct: employees are conditioned to act quickly on executive requests, especially when urgency is implied. The DSIT Cyber Security Survey confirms that impersonation attempts targeting senior leaders are now occurring simultaneously across email, WhatsApp, and other channels, representing a significant and growing threat to UK businesses.
1.2 How much does CEO fraud cost UK businesses?
According to UK Finance's Half-Year Fraud Report 2025, CEO fraud carries the highest average case value of all APP scam types, at just over £20,000 lost per confirmed case. These are reported figures only. Many organisations do not disclose incidents publicly, either due to reputational concerns or a lack of awareness that the fraud is reportable.
1.3 Why do existing security tools fail to stop executive impersonation fraud?
MFA confirms a login, not if the specific request is genuine. Email filters catch known patterns; they do not catch requests that are contextually accurate, tonally matched, and timed to coincide with live business activity. As the NCSC's guidance on Business Email Compromise makes clear, these attacks are crafted to appeal to specific individuals and can be even harder to detect because they target executives or budget holders and exploit established trust relationships.
1.4 How can businesses stop CEO impersonation fraud in real time?
UnDoubt Workforce adds mutual, cryptographic verification to internal communications so employees never have to guess whether a request is real. When a high-risk request arrives, a prompt is sent to the requester's trusted device. They approve or deny, the device signs the response, and the action either proceeds or is blocked, with your security team alerted.
2.0 Helpdesk Social Engineering
2.1 What is helpdesk social engineering and how do attackers use it to access your business?
An attacker contacts your IT helpdesk posing as an employee. They use researched personal details to pass basic identity checks. The helpdesk agent resets a password, enrols a new device, or changes account permissions. The attacker is now inside your organisation with legitimate, authenticated credentials.
Helpdesk staff are trained to be responsive. Their job is to solve problems quickly and reduce friction. That instinct, to help, to trust, to move efficiently, is precisely what attackers target. The attack requires no technical skill, only a credible story, a phone line, and background research largely available through LinkedIn and public company records. The most common helpdesk attack patterns include:
- Credential reset via impersonation. The attacker calls the helpdesk posing as an employee locked out of their account. They provide enough verifiable detail to pass security questions and have the password reset to a device they control.
- MFA bypass requests. Attackers claim to have lost access to their authenticator app and request enrollment of a new device, granting direct access without needing to compromise the original.
- Privilege escalation. Once a low-level account is compromised, the attacker contacts the helpdesk again, posing as a more senior employee to request elevated permissions or access to restricted systems.
- Third-party service desk targeting. Attackers target outsourced IT providers rather than the organisation directly, exploiting less stringent verification procedures and broader system access.
2.2 How much does a helpdesk social engineering attack cost an enterprise?
The financial damage extends well beyond the initial breach. Once inside, attackers move laterally, escalate permissions, and in the most severe cases, deploy ransomware across the entire estate. The DSIT Cyber Security Breaches Survey found that for medium and large UK businesses, the average cost of the single most disruptive breach was approximately £10,830. For organisations where a helpdesk breach provides authenticated access at scale, the exposure is substantially higher.
2.3 Why do standard helpdesk verification processes fail to stop impersonation?
Security questions can be researched. The personal details an attacker needs to pass a standard identity check, including name, role, manager, and recent system activity, are largely available through LinkedIn and company websites. The process helpdesk agents follow was designed to confirm that a caller knows certain facts. It was not designed to verify that the caller is actually the person those facts belong to.
Cifas's Fraudscape 2025 report highlights that criminals continue to use well-established impersonation tactics at speed and scale, with the threat amplified significantly by the use of AI and generative technologies that enable them to bypass security checks.
2.4 How can businesses protect their IT helpdesk from social engineering attacks?
UnDoubt Verify sends a real-time prompt to the employee's trusted device when a sensitive helpdesk request is made. The device signs the response cryptographically, giving agents verified confirmation before acting rather than a knowledge check that can be gamed. Available as Verify for one-way confirmation and Verify+ for higher-risk two-way interactions.
.jpg)
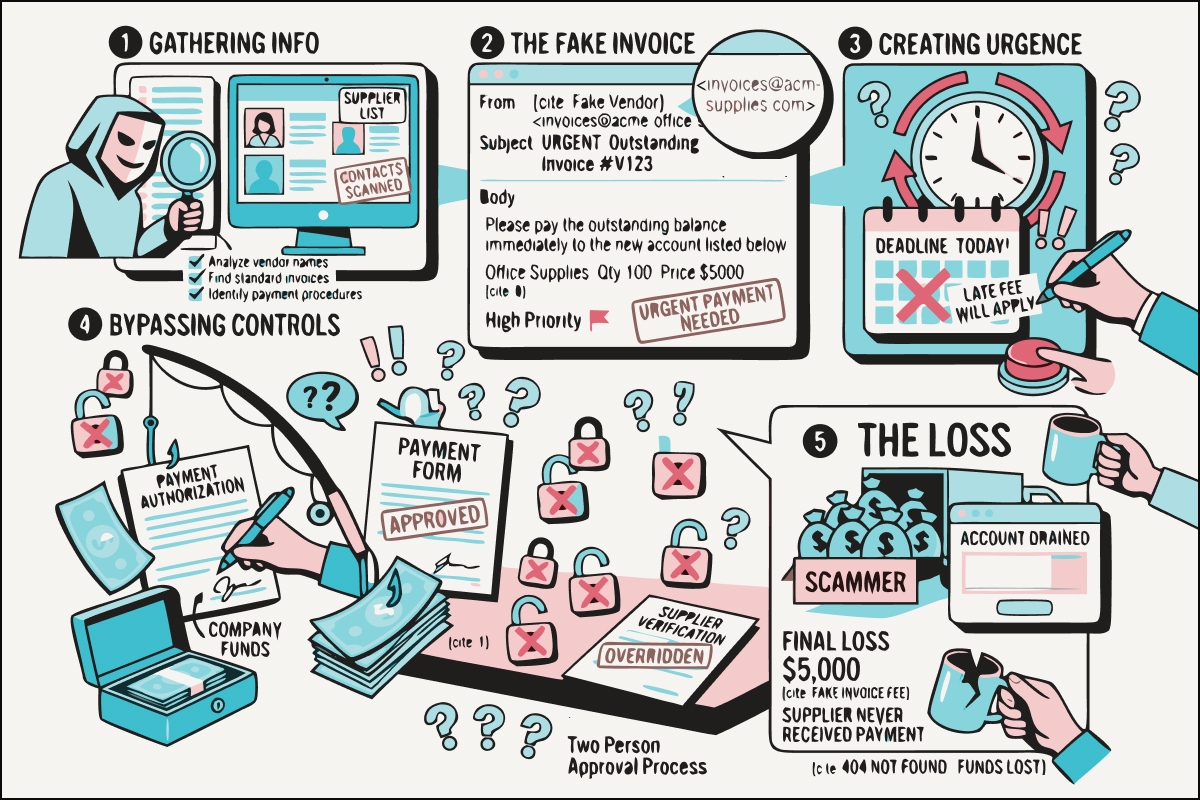
3.0 Vendor and Supplier Impersonation
3.1 What is vendor impersonation fraud, and how does payment diversion happen?
An attacker impersonates a known supplier, contractor, or business partner to redirect a payment. They intercept or replicate an active correspondence thread, introduce a plausible change, and wait for the payment to reach an account they control. The real supplier never receives the funds. This attack works precisely because it fits the context of real business. The email looks right. The request follows a real transaction. The timing is deliberate, typically aligned to a scheduled payment cycle or the close of a project. The most common forms include:
- Bank detail change requests. A message appearing to come from a known supplier requests that payment details be updated ahead of an upcoming invoice, framed as a routine administrative change.
- Invoice fraud. A near-identical invoice is submitted with minor changes such as a modified account number or slight variation in the sender address, timed to coincide with a genuine payment cycle.
- Email chain compromise. Attackers gain access to a real supplier email account and insert fraudulent instructions directly into an existing thread, with full visibility of previous correspondence and tone.
- Impersonation during supplier onboarding. Fraudsters target the onboarding process, submitting false payment details before proper verification procedures have been established.
3.2 How much does payment diversion fraud cost UK businesses?
According to UK Finance's Half Year Fraud Report 2025, criminals stole £629.3 million in the first half of 2025 alone, a 3% increase on the same period in 2024, across more than 2.09 million confirmed cases. Right-hand APP fraud losses specifically reached £257.5 million in the first half of 2025, a 12% increase year-on-year, with 66% of cases beginning on online platforms. Right-hand Vendor and supplier impersonation sits within the invoice and mandate fraud category, which UK Finance identifies as one of the fraud types most likely to affect businesses specifically.
3.3 Why do email and invoice checks fail to stop vendor impersonation fraud?
Domain checking and invoice verification confirm that a request looks right. They say nothing about whether the person who sent it is genuinely who they claim to be. An attacker who has compromised a real email account, or built a convincing lookalike domain, passes both checks. The DSIT Cyber Security Newsletter from March 2025 notes that monitoring supplier cyber security remains a low priority for most UK organisations, with formal supplier assessments having dropped from 28% to 23% year-on-year. Fortune The verification step that matters most is the one most businesses do not have.
3.4 How can businesses verify supplier communications before making a payment?
UnDoubt Connect adds a cryptographic verification layer to external communications. Before any high-risk action is taken, a prompt is sent to the originator's trusted device. They confirm, the device signs the response, and your team acts with certainty. Available as Connect for one-way verification and Connect+ for two-way confirmation on higher-risk interactions.
The Common Thread
All three of these scams succeed for the same reason: they exploit the gap between receiving a request and acting on it.
That gap is not a training problem. Training raises awareness. It does not change the fact that, at the moment of decision, employees and finance teams have no reliable way to verify that the person behind a request is genuinely who they claim to be.
Closing this gap requires infrastructure designed specifically for the moment of risk: real-time, mutual verification that confirms a request is genuine before any action is taken.
That is what UnDoubt is built to do.
Protect Your Organisation Before the Next Request Arrives
UnDoubt offers enterprise pilots across all three products:
UnDoubt Workforce - mutual, real-time verification for employees across voice, video, and email. Prevents CEO fraud, colleague deepfakes, and internal social engineering.
UnDoubt Verify - real-time confirmation for helpdesk and customer interactions. Confirms the human behind every sensitive request.
UnDoubt Connect - real-time verification for supplier and partner communications. Stops payment diversion and vendor impersonation before any risky action is taken.
Protect your highest-risk workflows. Contact us at undoubt@lastingasset.com to discuss a pilot tailored to your organisation.
.jpg)
Workplace Scams FAQs
1. How do I know if my business has been targeted by CEO fraud?
CEO fraud often goes undetected until after a payment has been made. Warning signs include unexpected requests from senior leaders via personal email or messaging apps, unusual urgency around transfers, instructions to skip normal approval steps, and requests arriving outside of working hours. If something feels off, verify it through a separate channel before acting.
2. How can businesses protect themselves from CEO fraud and invoice fraud?
The most effective protection is verifying high-risk requests through a secure channel before any payment, access, or approval is granted. UnDoubt is building an enterprise-grade verification solution for exactly this purpose, covering helpdesk requests, payment approvals, and internal communications.
3. What is the difference between phishing and social engineering?
Phishing is a specific technique, typically a deceptive email designed to steal credentials or direct someone to a malicious site. Social engineering is the broader category: any method that manipulates a person into taking an action or revealing information. CEO fraud, helpdesk impersonation, and vendor scams are all forms of social engineering. They rely on psychology and established trust rather than technical exploits, which is why traditional security tools often fail to detect them.
4. What is authorised push payment fraud, and how does it affect UK businesses?
Authorised Push Payment fraud occurs when someone is manipulated into voluntarily transferring money to an account controlled by a fraudster. Because the victim authorises the payment themselves, it is harder to reverse than unauthorised fraud. According to UK Finance's Half Year Fraud Report 2025, APP fraud losses reached £257.5 million in the first half of 2025 alone, a 12% increase on the same period the previous year.
5. How Is UnDoubt different from MFA or standard identity verification?
Standard MFA confirms that someone has access to a device or account at the point of login. It says nothing about whether the requests that follow are genuine. UnDoubt verifies the human behind a specific request, at the moment that request is made, using out-of-band cryptographic confirmation from a trusted device. It addresses the gap between authentication and action that existing tools leave open.
References
- UK Finance. (2025). Annual Fraud Report 2025. https://www.ukfinance.org.uk/news-and-insight/press-release/fraud-report-2025-press-release
- UK Finance. (2025). Half-Year Fraud Report 2025. https://www.ukfinance.org.uk/policy-and-guidance/reports-and-publications/half-year-fraud-report-2025
- Cifas. (2025). Fraudscape 2025: Reported fraud hits record levels. https://www.cifas.org.uk/newsroom/fraudscape-2025-record-fraud-levels
- Department for Science, Innovation and Technology and Home Office. (2025). Cyber Security Breaches Survey 2025. https://www.gov.uk/government/statistics/cyber-security-breaches-survey-2025/cyber-security-breaches-survey-2025
- Department for Science, Innovation and Technology. (2024). Cyber Security Breaches Survey 2024. https://www.gov.uk/government/statistics/cyber-security-breaches-survey-2024/cyber-security-breaches-survey-2024
- Department for Science, Innovation and Technology. (2025). Cyber Security Longitudinal Survey: Wave Five Results. https://www.gov.uk/government/publications/cyber-security-longitudinal-survey-wave-five-results/cyber-security-longitudinal-survey-wave-five-results
- Department for Science, Innovation and Technology. (2025). DSIT Cyber Security Newsletter: March 2025. https://www.gov.uk/government/publications/dsit-cyber-security-newsletter-march-2025/dsit-cyber-security-newsletter-march-2025
- National Cyber Security Centre. (2024). Business Email Compromise: Payment Diversion Fraud. https://www.ncsc.gov.ie/pdfs/NCSC_BEC_Guidance.pdf


.png)