Social Engineering vs Hacking: Why One Is Now Far More Dangerous Than the Other
Most people picture a hacker as someone in a dark room, writing code at speed, breaking through firewalls and cracking encryption. That image was never entirely accurate, and today it is almost entirely wrong.
The fraud that is costing businesses and individuals the most money in 2026 does not involve breaking into systems at all. It involves calling the right person, saying the right things, and being believed.
This is social engineering. And if you run a business, manage a team, or simply use the internet in your daily life, understanding the difference between this and traditional hacking is one of the most important things you can do right now.
What Is Social Engineering? And How Is It Different from Hacking?
Hacking, in the traditional sense, is when someone exploits a weakness in technology. They find a flaw in software, a misconfigured server, or a poorly protected network, and they use that flaw to get inside. It is technical, it requires skill, and good security software can often detect and stop it.
Social engineering is something entirely different. It exploits people rather than systems. A social engineer does not need to crack your password. They persuade you to hand it over. They do not need to bypass your firewall. They convince someone inside your organisation to open the door for them.
The name sounds abstract, but the attacks are not. They look like:
- A phone call from "your bank" asking you to confirm your account details before an urgent block is placed.
- An email from "your CEO" requesting a same-day payment to a new supplier account.
- A message from "IT support" telling you your password has expired and you need to reset it immediately.
- A caller to your company's helpdesk, impersonating a colleague, asking for their account to be unlocked.
None of these requires any technical hacking at all. They only require that the target trusts the request enough to act on it.
Why Are Social Engineering Attacks Outpacing Traditional Hacking?
For years, hacking and social engineering existed as roughly equal threats. Criminals used both. Now, the balance has shifted significantly.
Drawing on more than 700 incident response cases globally, Unit 42's 2025 Global Incident Response Report: Social Engineering Edition found that social engineering accounted for 36% of all cyber intrusions between May 2024 and May 2025, surpassing malware and software vulnerabilities as the leading method of attack. The same research found that social engineering incidents were far more likely to result in data exposure than other attack vectors, affecting 60% of the cases studied.
There are three main reasons this shift has happened, and they are all connected to the rise of artificial intelligence.
Impersonation has become cheap. Until recently, pulling off a convincing impersonation at scale required significant time, research, and skill. Criminals had to write believable scripts, craft convincing emails, and research their targets manually. Generative AI can now produce a believable phishing message in minutes.
Detection has become harder. We have always relied on familiarity as a safety check. If a voice sounds right, if an email looks professional, if someone knows the right details, we tend to trust them. AI has broken this. Voice cloning tools can now replicate a person's speech from a 3-second audio sample. Attackers are using AI-generated voice clones and even live deepfake video feeds to make themselves indistinguishable from the people they are impersonating.
The scale of attacks has exploded. Social engineering is now the primary attack vector across enterprise environments. The Verizon 2025 Data Breach Investigations Report confirms that the human element remains a consistent factor in the majority of serious breaches, with social engineering and stolen credential continuing to dominate as the leading initial access methods year-on-year.

IT Helpdesk Impersonation: The Most Exploited Entry Point in Your Business
If you run a business or work within one, there is a specific vulnerability that deserves your full attention: your IT helpdesk or customer support.
Helpdesk agents are trained to help. Someone calls with a problem, and the agent resolves it. That instinct, which is entirely right in normal circumstances, becomes a liability when the caller is not who they claim to be.
Bad actors have identified internal IT helpdesks as a critical weak point in enterprise cybersecurity. Threat clusters like Scattered Spider use social engineering tactics to trick support agents into resetting victim account credentials, effectively bypassing multi-factor authentication and other security measures.
Marks & Spencer is the example most often cited, and rightly so. In April 2025, M&S disclosed a ransomware attack after hackers duped its IT helpdesk into resetting employee credentials. Co-op revealed that limited member data had been accessed after a helpdesk social engineering attack, and Harrods confirmed attempted unauthorised access to its systems. The UK Cyber Monitoring Centre classified the M&S and Co-op incidents as a single combined cyber event, estimating the total financial impact across affected parties at £270 million to £440 million.
These are not small, poorly resourced companies. They have dedicated IT teams, security policies, and training programmes. None of that was enough because the attackers bypassed the technology entirely and targeted the people.
How a Social Engineering Attack Unfolds: Step by Step
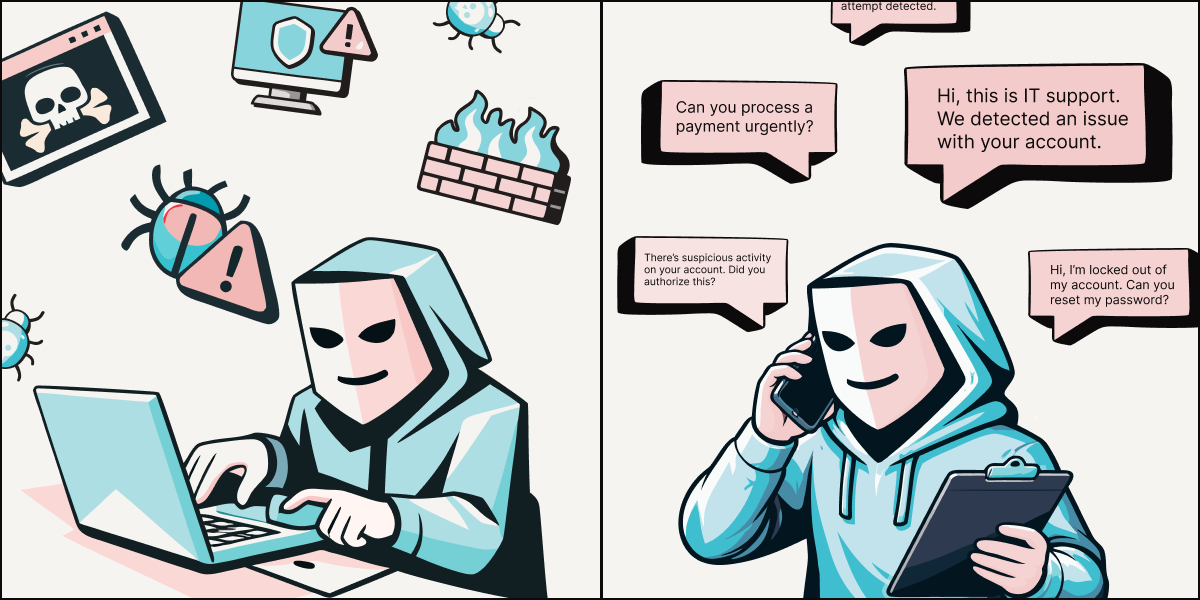
Understanding the sequence helps you recognise it in practice.
- Stage one: research. The attacker gathers information. LinkedIn shows them your job title, your manager's name, and how long you have worked at the company. Your company website gives them the support number and perhaps the name of your IT team. Data that feels harmless in isolation becomes a convincing script in the wrong hands.
- Stage two: contact. They call or message, impersonating a legitimate person. They use the right name, the right tone, and enough specific detail to seem credible. They create urgency: a system is down, a deadline is approaching, a security alert has been triggered.
- Stage three: exploitation. The helpdesk agent, customer service representative, or colleague acts on the request. A password is reset. An MFA device is changed. Access is granted. By the time anyone realises what has happened, the attacker has already deployed ransomware.
Social Engineering Prevention: Common Mistakes Businesses Keep Making
Assuming awareness training is enough. Security awareness programmes matter, but they address the wrong part of the problem. Training teaches people to spot suspicious behaviour. Social engineering is specifically designed not to look suspicious. A well-researched impersonation call does not trigger alarms; it feels like a normal working day.
- Relying on knowledge-based verification. Most helpdesks still verify identity by asking questions: date of birth, employee number, last four digits of a phone number. Attackers gather employee details from public sources, including social media, company websites, and data breaches, to create a believable persona. The answers to your verification questions are often findable. They are not proof of identity.
- Treating the helpdesk as a low-risk function. Support teams and helpdesks have significant power: they can reset passwords, disable security controls, and grant access to systems. That power, without a reliable verification, makes them one of the highest-risk points in any organisation.
- Moving too fast under pressure. Urgency is a social engineer's most-used tool. When someone says a system is down and a team is waiting, the instinct is to move quickly. That instinct can override the caution that would otherwise prompt someone to verify a request properly.
How UnDoubt Verify Stops Helpdesk Social Engineering Attacks in Real Time
The organisations that suffered the biggest losses recently were not unprepared in the conventional sense. They had IT teams, policies, and training. What they lacked was a way to verify, in real time, that the person on the other end of a call or message was genuinely who they claimed to be.
That gap is now closeable. UnDoubt Verify lets customers confirm they are genuinely communicating with your organisation during calls or messages, before they share sensitive information or act on a request. Depending on the level of risk, it can confirm one side of the interaction (UnDoubt Verify) or require both parties to verify each other before any sensitive action proceeds (UnDoubt Verify+).
For helpdesks, this changes the verification dynamic entirely. Instead of relying on knowledge-based questions that an attacker could have researched, the verification happens in real time, across voice and messaging channels, and is cryptographically confirmed. The agent does not have to trust their instincts about whether a caller sounds right. They have a clear, reliable signal.

Sources:
[1] Unit 42, Palo Alto Networks, 2025 Global Incident Response Report: Social Engineering Edition, July 2025 https://unit42.paloaltonetworks.com/2025-unit-42-global-incident-response-report-social-engineering-edition/
[2] Verizon Business, 2025 Data Breach Investigations Report, April 2025 https://www.verizon.com/business/resources/reports/dbir/
[3] BleepingComputer, MGM Resorts ransomware attack led to $100 million loss, data theft, October 2023 https://www.bleepingcomputer.com/news/security/mgm-resorts-ransomware-attack-led-to-100-million-loss-data-theft/
[4] Infosecurity Magazine, M&S and Co-op Hacks Classified as Single Cyber Event, 20 June 2025 https://www.infosecurity-magazine.com/news/ms-coop-hacks-single-event/
[5] CyberScoop, Social engineering attacks surged this past year, Palo Alto Networks report finds, August 2025 https://cyberscoop.com/social-engineering-top-attack-vector-unit-42/
[6] Infosecurity Magazine, How the UK Retail Sector Responded to the Scattered Spider Hack Wave, December 2025 https://www.infosecurity-magazine.com/news-features/how-uk-retail-responded-hack-wave/


.png)